The Security Awareness Company is now part of the KnowBe4 family! For more information read our press release here
Keep your messaging fresh and in the forefront of your users’ minds with content that reinforces the lessons most important to your organization.
Reinforcement content is not scored nor usually tracked in a formal way, and information is conveyed through a variety of modalities to appeal to different types of users. You will find that when you employ reinforcements successfully, users will learn about twice as much as they would from more traditional, formal training.
This type of content includes monthly newsletters, security video modules, and Security Documents.
Our popular magazine-quality newsletter offers you an easy way to keep your staff up-to-date on policies and best practices. By presenting important information in a non-technical, conversational tone that appeals to a wide variety of audiences, we make security awareness easy to understand (and fun to read!).
Consistency is vital to the success of any awareness program. Monthly newsletters are a proven way to reinforce and create this consistency!
Reminding users of important messages and policies each month in an approachable, fun manner will help you take strides towards establishing a strong culture of learning and security awareness within your organization, as well as leveraging more informal learning opportunities.
Now available in over 35 languages!

Each month, our content is written according to a list of topics we release before the beginning of each year.* This allows the newsletter to remain current while focusing on all of the important issues.
We recommend planning your entire year’s security awareness program around these topics, providing microlearning opportunities (such as posters, games, or videos) along with the newsletter. We often cover the same topics every 12-18 months, addressing them from a different perspective or angle.
* Topics are subject to change based on important infosec issues and/or to stay relevant with up-to-date news.
Jan: The Foundations of Security Awareness
Improving a skill set requires focusing on the fundamentals of what makes people great at their craft. Security awareness is no different. This edition highlights the basic concepts of awareness and why it’s vital to maintaining security and privacy for every member of an organization.
Feb: The Dangers of Malware
Malware infections can result in stolen data, identity theft, and, in the case of ransomware, a staggering amount of financial loss. That’s why everyone needs to understand what malware can do, how it spreads, and how to avoid it.
Mar: Data Breach Basics
Major data breaches impact millions of people worldwide and can have long-term consequences for everyone involved. Avoiding those breaches is a top priority for every organization and individual. This issue refreshes the basics of how those breaches happen and how they can be prevented.
Apr: Confidentiality, Integrity, and Availability
Confidentiality, integrity, and availability represent the three pillars of security. They provide a comprehensive strategy that helps organizations protect data and people. By understanding how the three pillars work together, every individual can improve their security posture.
May: Remote and Mobile Security
Security awareness is not a location-based concept. It applies to every environment, whether that involves traveling or working from home. Regardless of where someone goes, it’s important to protect smart devices, travel safely, and take security awareness along for the ride.
Jun: Spear Phishing: When Attackers Get Personal
Not every phishing attack is equal. Some are generic and distributed to large groups of people all at once. Others, however, are much more intentional and target specific individuals or organizations. This month’s issue takes a deep dive into the advanced techniques cybercriminals use in spear phishing attacks.
Jul: Warning Signs: Identifying Attacks
Social engineers use various techniques to defraud people of money or convince someone to divulge confidential information. The key to identifying their attacks is knowing what warning signs to stay alert for and what to do when encountering them.
Aug: Securing the Physical Domain
Protecting information and maintaining security isn’t a complicated process. Nor is it limited to circumventing cyberattacks. There’s also a physical side to security involving nontechnical approaches that play a big role in safeguarding people, devices, and data.
Sep: Zero Trust Security
The zero trust security model is built on the concept of “never trust; always verify.” This means nothing is inherently trusted at any point, and everything is always verified, often continuously. This issue applies that mindset to all things related to security awareness.
Oct: Ransomware Realities: What Everyone Needs to Know
There is no doubt that ransomware attacks are among the top concerns for organizations in nearly every industry. From staggering financial losses to costly downtime, it’s vital that everyone gain a firm understanding of just how dangerous this form of malware is and how to avoid digital lockdowns.
Nov: Responding to Incidents
One key goal of every organization is to avoid security incidents that lead to breaches, malware infections, and other unwanted consequences. Unfortunately, incidents may happen. How people respond to them could be the difference between a minor event and a major complication.
Dec: Protecting Your Digital Identity
With enough personal details, scammers can steal someone’s identity and use it to perform a variety of scams. Victims of identity theft often face a difficult recovery process ranging from stolen money to destroyed credit ratings. It’s a personal crime that requires a commitment to ensuring private information remains private.
1-5 minute security “bytes” that cover a broad range of topics and include a wide variety of styles. These are great to use every month to keep security in the forefront of your employees’ minds.
Video reinforcements are an easy way to create informal learning opportunities for your employees. Short, focused, to-the-point, videos don’t require assessments and feel less like training and more like how your users already interact online.
Security Video Bytes
Security video bytes, like our Cyber Confessions Series, make a great addition to any security awareness training program and will give your users lots of informal microlearning opportunities!
Our current collection of 70+ security video modules are created in a broad variety of styles, from animated scenarios based on true stories to educational documentary style using stock footage. They all provide practical action items and lessons your users can apply both at work and at home.
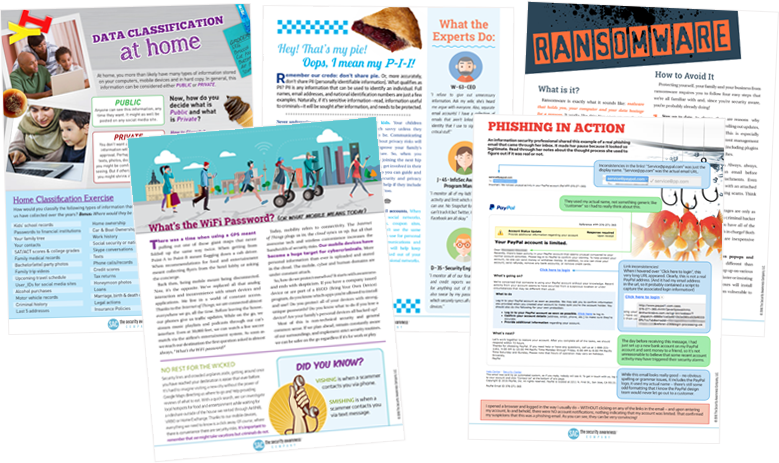
Security Documents can help keep your users engaged in your security awareness training program!
The key to creating a successful information security awareness training program is to reinforce key messages as often as possible. To do this, you must catch your users’ attention and hold it. That’s where our versatile Security Documents come in!
Security Documents are standalone pages, designed to be eye-catching enough to grab employees’ attention to create teachable moments outside formal learning. These are delivered as PDFs and can be used in a variety of creative ways. You can add these pages onto any other PDF (such as a newsletter or policy document), print them out to use as flyers in bathroom stalls or elevators, or combine them to create a customized magazine on a specific subject. It’s up to you!
© KnowBe4, Inc. All rights reserved. | Legal | Privacy Policy | Terms of Use | Security Statement